Shared and resource mailboxes in Microsoft 365 are designed for collaboration, not for direct sign-ins. However, if sign-in remains enabled, attackers could exploit these accounts to bypass security policies, send unauthorized emails, or access confidential data—posing a serious compliance and security risk. As an admin, you must properly secure these mailboxes to prevent misuse and safeguard sensitive data.
Therefore, this blog will guide you to identify and block shared mailbox sign-in in your Microsoft 365 environment before they become a security risk.
Review and Block Sign-in for Shared Mailbox in Microsoft 365
You can check the sign-in status of shared and resource mailboxes in the Microsoft 365 admin center. However, manually verifying each mailbox is difficult and time-consuming.
To simplify this process, we have developed a PowerShell script. This script lets you generate a report on the sign-in status of shared and resource mailboxes in Microsoft 365. Upon your confirmation, the sign-in will also be blocked. Sounds easy, right? Disable direct mailbox logins in one step—no switching between tabs, no waste of time.
Note: By default, the script checks shared, room, and equipment mailboxes. You will have the option to block sign-in to specific mailbox type.
Script Highlights:
- Export sign-in status report for all the resource and shared mailboxes into a CSV file, including:
- Shared mailboxes – Check sign-in settings for shared accounts.
- Room mailboxes – Track sign-in configurations for meeting rooms.
- Equipment mailboxes – Review sign-in status for assigned equipment.
- Blocks sign-in for all shared mailboxes upon confirmation.
- Allows to verify sign-in configuration for specific mailbox types and blocks them.
- The script automatically verifies and installs the Exchange Online PowerShell and Microsoft Graph Beta modules (if not installed already) upon your confirmation.
- Allows users to modify the generated CSV report and provide it as input later to block the sign-in on respective mailboxes.
- Provides a detailed log file after disabling sign-in for shared and resource mailboxes.
- The script can be executed with an MFA-enabled account too.
- The script supports Certificate-based authentication (CBA).
Download Script: BlockSigninForSharedAndResourceMailbox.ps1
Shared Mailbox Sign-in Status Report – Sample Output
The exported ‘shared mailbox sign-in status’ report looks like the screenshot below.
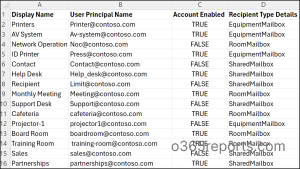
The exported report contains shared and resource mailboxes with additional attributes info like,
- Display Name
- User Principal Name
- Account Enabled
- Recipient Type Details [Shared/ Room/Equipment Mailbox]
Once the report is generated, you’ll be prompted to confirm whether you want to block sign-in for the mailboxes listed in the CSV report.
To proceed, enter ‘Y’ to disable sign-in for all room, equipment, and shared mailboxes included in the report, as shown below.

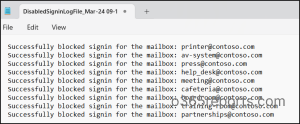
Once sign-in is disabled, you will get a txt log file for output as below.
Block Shared Mailbox Sign-in in Microsoft 365 Using PowerShell – Script Execution Methods
- Download the script.
- Start the Windows PowerShell.
- Select any of the methods provided to execute the script.
Method 1:
Execute the script with MFA or non-MFA account.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 |
Method 2:
You can explicitly pass credentials (username and password) and execute the script.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 -Username <UPN> -Password <Password> |
The above method supports only non-MFA accounts. If the admin account has MFA, you need to disable MFA using CA policy to make this work.
Method 3: Run the script using certificate-based authentication.
To use certificate-based authentication, you must register the app in Entra ID which helps you to connect Exchange Online using certificate.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 -Organization <Domain> -ClientId <AppId> -CertificateThumbprint <CertThumbPrint> |
Depending on the requirements, you can use either CA certificates or create self-signed certificates.
Find and Disable Shared Mailbox Logins in Microsoft 365
Utilize the PowerShell script to find all the sign-in enabled shared mailboxes and disable them to enhance security. Explore more use cases you can achieve using the script below.
- Report and block resource & shared mailbox sign-in in Microsoft 365
- Disable shared mailbox sign-in using PowerShell
- Disable sign-in for specific shared and resource mailboxes
- Verify and block sign-in on room mailboxes
- Find and disable sign-in for equipment mailboxes
Report and Block Resource & Shared Mailbox Sign-in in Microsoft 365
When managing resource and shared mailboxes, identifying sign-in enabled accounts is crucial to preventing unauthorized access. To find all shared and resource mailboxes with sign-in enabled and disable them, run the following command.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 |
What to do next?
- By reviewing the exported CSV report, you can assess which mailboxes require sign-in to be disabled based on your security policies.
- If you confirm, the script will disable sign-in ability and send you a log file with result status details.
Disable Shared Mailbox Sign-in Using PowerShell
Shared mailboxes allow multiple users to manage emails collectively, such as for product feedback or a Catch-All mailbox. While users need an Exchange Online license to access them, the shared mailbox itself doesn’t require one.
If a user unintentionally signs in with a shared mailbox account, it becomes a non-compliant mailbox, violating Microsoft’s licensing policy. To resolve this, you can remove license from that shared mailbox and block sign-in.
By default, the account status is set to Enabled, allowing users to login. To disable sign-ins particularly for shared mailboxes alone, run the script with the –SharedMailboxOnly parameter.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 -SharedMailboxOnly |
This execution exports the sign-in configuration status report and (excluding resource mailboxes) and, upon your confirmation, disables the sign-in into shared mailboxes option.
Disable Sign-in for Specific Shared and Resource Mailboxes
If you want to block sign-in configuration only for specific shared and resource mailboxes, you can prepare a CSV file with a list of required mail addresses.
Now, replace <FilePath> with the path of your CSV file in the -CSV parameter to check the sign-in status of multiple shared and resource mailboxes.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 -CSV <FilePath> |
Ensure that the column containing users’ UPN is named User Principal Name, as shown in the image below. The script will then check the sign-in status of the specified mailboxes and export the results as the report for verification.
Sample Input:
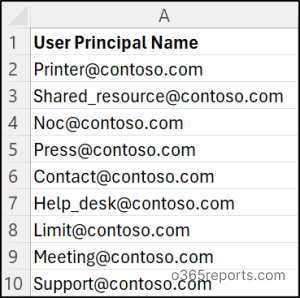
Tip: You can also modify and use the output CSV report generated by this script as an input to block sign-in of desired shared and resource mailboxes.
Verify and Block Sign-in on Room Mailboxes
A room mailbox in Microsoft 365 is a resource mailbox designed solely for scheduling physical spaces like conference rooms. Since it doesn’t require a license, users shouldn’t log in directly. However, if sign-in remains enabled, it could be exploited to gain unauthorized access or be misused for unintended activities. Blocking sign-in ensures room mailboxes function strictly for reservations, preventing security loopholes.
So, to verify whether sign-in is enabled for room mailboxes, run the script with the -RoomMailboxOnly parameter, as shown below.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 -RoomMailboxOnly |
The above script execution returns sign-in status of all the room mailboxes in your organization. It helps to easily narrow down the desired result and block login to the room mailbox account.
Find and Disable Sign-in for Equipment Mailboxes
Equipment mailboxes ensure seamless booking of shared hardware, such as projectors, conference phones, etc. However, if sign-in is enabled, users could log in directly and modify or cancel existing reservations, leading to scheduling conflicts and operational disruptions. Disabling sign-in prevents unauthorized changes, ensuring resource bookings remain intact.
To achieve this, you can run the script by adding the –EquipmentMailboxOnly parameter.
|
1 |
.\BlockSigninForSharedAndResourceMailbox.ps1 -EquipmentMailboxOnly |
The above exports the sign-in status of all the equipment mailboxes in your Microsoft 365 environment and allows you to block sign-in for those with login enabled.
Effortlessly Track Shared Mailbox Sign-in Status with AdminDroid!
AdminDroid’s Exchange Online Reporter provides shared mailbox reports that instantly displays the sign-in status of all shared mailboxes. Not just you can view the sign-in status, you can dive deeper! Like, filter, customize, schedule, and export reports to proactively mitigate security risks and prevent unauthorized access.
Beyond that, this tool simplifies mailbox monitoring by providing actionable reports on mailbox activity and access patterns. With AdminDroid, you gain in-depth visibility into shared mailbox access through the following reports:
- Shared mailbox sign-in activities report
- Shared mailbox members report
- Licensed shared mailbox report
- Non-compliant shared mailbox report
- Shared mailbox permission details report and more.
This Microsoft 365 management solution enhances Exchange Online security with 65+ detailed auditing reports covering mailbox activities, permission changes, and configuration updates.
From a single interface, track mailbox utilization, storage, and audit settings, empowering admins with real-time insights for better management. Optimize your Exchange Online security and efficiency—try AdminDroid today and take control of your shared mailboxes access!
Securing shared mailboxes is a crucial step in strengthening your Microsoft 365 environment. We hope this blog helps you identify the sign-in allowed shared mailboxes and block them effectively. Drop your queries in the comment section.