Office 365 admins can configure permissions to delegate access to other mailboxes. Since mailboxes contain sensitive data, it’s required to monitor mailbox permission changes to ensure security and prevent data leakage.
How to Audit Mailbox Permission Changes in Exchange Online:
Mailbox permission can be granted in the following ways.
- Full access: Delegate can read, modify, and delete content from the delegated mailbox.
- Send as: Delegates can send email from the delegated mailbox, which appears to be sent by the mailbox owner.
- Send on behalf: Delegates can send emails from a delegated mailbox on behalf of the mailbox owner.
To detect mailbox permission changes, you can use ‘Audit log search’ or the PowerShell cmdlet ‘Search-UnifiedAuditLog.’ Since each mailbox permission should be tracked individually, it’s challenging to perform through UI. Also, you can’t filter out send on behalf permission changes through the Audit log search.
How to Track Mailbox Permission Changes using PowerShell:
With PowerShell, admins can track Exchange mailbox permission changes easily. However, it’s hard to filter out send on behalf permission changes, as it comes with other property changes. Worry not! We have created a PowerShell script to monitor permission changes at ease. The script allows you to generate an audit report on all permission changes or specific permission changes. Let’s dive in!
Known limitation: For ‘send on behalf’ permission removal, Microsoft doesn’t provide the name of the delegate whose access is removed. Instead, it will show the current delegates after the latest modification. We have handled this special case in our script.
Also, admins can configure alert policy to get notified when admins assign mailbox permissions.
Script Download: AuditMailboxPermissionChanges.ps1
Script Highlights:
- The script uses modern authentication to retrieve audit logs.
- The script can be executed with an MFA enabled account too.
- Exports report results to CSV file.
- Excludes system generated permission changes by default.
- Helps to detect who modified mailbox permissions.
- Tracks who granted full access, send as, send on behalf permissions separately.
- Allows you to generate mailbox permission changes audit report for a custom period.
- Automatically installs the EXO V2 module (if not installed already) upon your confirmation.
- The script is scheduler-friendly. i.e., Credential can be passed as a parameter instead of saving inside the script.
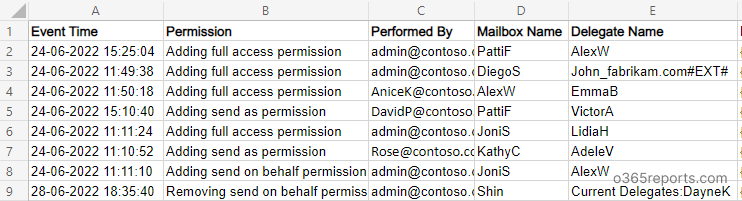
Sample Output:
The exported report will contain the following attributes: Event Time, Operation, Performed By, Mailbox Name, Delegate Name, and Additional Audit Data.
Script Execution Methods:
To run the script, you can choose any one of the methods below.
Method 1: Execute script with MFA and non-MFA account
|
1 |
.\ AuditMailboxPermissionChanges.ps1 |
The exported audit report contains all mailbox permission changes in the last 90 days.
Method 2: Execute script by explicitly mentioning the credentials (Scheduler friendly).
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -UserName admin@o365reports.com -Password XXX |
If the admin account has MFA, then you need to disable MFA based on the Conditional Access policy to make it work.
More Use Cases of ‘Audit Mailbox Permission Changes Script’:
Our script supports built-in filtering params to generate more granular audit reports based on your requirements. We have listed a few use cases below.
- Track mailbox permission changes
- Mailbox permission auditing for a custom period
- Detect who granted full access permission
- Detect mailboxes’ send as permission changes
- Find send on behalf permission changes
- Get monthly report on mailbox permission modification
- Schedule mailbox permission audit report
- Track mailbox delegation to external users
Track Mailbox Permission Changes:
The script will list all the mailbox permission changes, such as adding and removing full access permissions, send as permissions, send on behalf permissions for the last 90 days.
|
1 |
.\ AuditMailboxPermissionChanges.ps1 |
Note: Along with mailbox permission changes, You can also verify mailbox folder permissions for securing your mailboxes.
Mailbox Permission Auditing for a Custom Period:
By using –StartDate and –EndDate parameters, admins can generate mailbox permission auditing report for a custom period such as, last 7 days, 30 days, or any custom period.
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -StartDate 6/15/22 -EndDate 6/30/22 |
The above example retrieves all the mailbox permission changes between June 15, 2022, and June 30, 2022.
Detect who Granted Full Access Permission:
To detect who gave full access permission to edit, modify, delete content from others’ mailbox, you can run the script with –FullAccessOnly parameter. If any unwanted assignments are found, consider removing full access permissions from those mailboxes.
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -FullAccessOnly |
The exported report will contain the full access permission changes that happened in the past 90 days. You can also use, -StartDate and –EndDate param to generate a report for custom period.
Monitor Mailboxes’ Send as Permission Changes:
When a user is granted send as permission, they can send email as delegated mailbox – even without mailbox owner’s knowledge. So, it’s challenging to track send as emails. Hence, admins need to keep an eye on send as permission changes. To find who granted and removed send as permissions, run the script with –SendAsOnly switch param.
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -SendAsOnly |
Find Send on Behalf Permission Changes:
‘Send on behalf’ permission changes have to be tracked in a different way. Also, Microsoft doesn’t provide delegate names directly in this case. It will show all the delegates’ names who have ‘send on behalf’ permission after the latest permission change.
Our script processes a few filters and retrieves the delegate name to whom the permission was assigned. But there is no way to retrieve the delegate name during send on behalf removal.
To track send on behalf permission changes, execute the script with the –SendOnBehalfOnly switch parameter.
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -SendOnBehalfOnly |
Schedule Mailbox Permission Audit Report:
Since the ‘Search-UnifiedAuditLog‘ can keep an audit log for 90 days (for E3 license), you may require old data for analysis. In that case, scheduling will help you keep the audit log for a longer period.
To automate the PowerShell script, you can use the below format in the Windows Task Scheduler.
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -UserName admin@o365reports.com -Password XXX |
If the admin account has MFA, you need to disable MFA based on the Conditional Access policy to make it work.
Get a Monthly Report on Mailbox Permission Changes:
To get a monthly report on deleted emails, run the script as follows,
|
1 |
.\ AuditMailboxPermissionChanges.ps1 -StartDate ((Get-Date).AddDays(-30)) -EndDate (Get-Date) -UserName admin@o365reports.com -Password XXX |
You can also use the above format to get scheduled monthly reports.
Track Mailbox Delegations to External Users:
In some situations, admins need to give mailbox access to external users. So, it is a critical task to identify who delegated mailbox access to whom. To track mailbox permission changes on external users, open the report with Excel and filter the ‘Delegate Name’ column that contains “#EXT#”.
Audit Mailbox Permission Changes Efficiently with AdminDroid
Granting mailbox permissions are unavoidable situation, but sometimes it might lead to elevated privileges, configuration errors, etc. While auditing these permissions using PowerShell can provide valuable insights, it may not always be the most efficient! For example, auditing mailbox permission changes using PowerShell often require complex and lengthy commands, which makes it time-consuming. Also, the process can be resource-intensive while auditing a large number of mailboxes.
So, if you’re seeking to improve your mailbox permission management, then check out the Exchange Online mailbox permissions reports by AdminDroid, you’ll be surprised for sure! The comprehensive reports provide valuable insights and metrics to help streamline your mailbox permission monitoring and auditing processes.
Wondering why AdminDroid is a Top Choice for Exchange Online Management?
- Export anywhere, in any format! You can export every Exchange Online report in various formats such as CSV, HTML, and PDF with just a click to analyze with greater flexibility.
- Schedule and sit back – Effortlessly set up automated schedules for daily monitoring reports like mailbox usage, spam & malware detections and receive real-time reports straight to your inbox. You won’t have to check reports manually anymore!
- Refine data intelligently – Now, you can merge multiple reports and apply additional filters, sorting, and columns for more effective mailbox traffic analysis.
- Delegate and share the load –Delegate access to reports, dashboards, tenants, etc., and work collaboratively. So that multiple team members can share the load of managing your Exchange Online environment.
- Don’t just crunch data in tables; visualize in charts! Visualize reports beyond the numbers & tables with our graphical AI charts. (Geo-map and heat map visualization). This makes it easier than ever to identify mailbox usage patterns and trends within an organization.
- Tenant management made easy – Manage multiple M365 tenants and get a bird’s eye view of everything in a single portal.
AdminDroid Exchange Online reporting tool covers over 170+ Exchange Online reports that help to track mailbox permissions changes, mailboxes with delegated access, guest access to mailboxes, and more. With these reports, admins can quickly identify who has access to sensitive information and take action instantly. Have a quick look at the different mailbox delegated permission reports by AdminDroid:
Mailbox permission report.
- Mailbox permission summary
- Mailbox with send as permission
- Mailbox with send on behalf permission
- Mailbox with full permission
- Mailbox with read permission
- Access to other mailbox reports
Mailbox permission changes
- Mailbox permission changes
- Mailbox folder permission changes
- Public folder permission changes
- Send As permission changes
Admins Mailbox access
- Admin Mailboxes access to other mailboxes
- Admins Mailboxes with Send As permission
- Admins Mailboxes with Send on Behalf permission
- Admins Mailboxes with Full Access permission
Guest Mailbox permissions
- Guests’ mailbox permission summary
- Guest access to other mailboxes


Overall, the AdminDroid Exchange Online management tool is a powerful reporting solution that provides organizations with detailed insights into their Exchange Online environment. Moreover, the free Azure AD reporting tool contains 120+ reports which provide a comprehensive view of the organization’s groups, group membership changes, users, licenses, user logins, password changes, etc. When it comes to auditing and reporting, you can be sure, AdminDroid has you covered.
Want to experience the power of AdminDroid in real-time? Try AdminDroid now with a 15-day free trial!
Conclusion:
Identifying who can access other mailboxes is one of the vital tasks in mailbox permission management. To get mailbox permissions for all the mailboxes, you can generate mailbox permission report. Alternatively, you can get a list of mailboxes a user has access to using our dedicated script.
I hope this blog is helpful for managing mailbox permissions in Exchange Online. If you have any queries, reach us through the comment section.