Hey Techies! Microsoft having deprecated its Baseline policy, it’s time to say hello to the newly introduced Security Defaults that replaces Baseline Policy. Through Security Defaults Microsoft aims at providing maximum security for the users whose primary goal is to set up an environment of business convenience, with less regards to security. Especially for those who do not prioritize security as their primary concern.
In this blog we walk you through: –
- How far this feature will help the newbies.
- What difference will it make for the existing users?
Through this blog, we aim to answer all your doubts on Security Defaults.
Major objective of Security Defaults.
Technology being the major chord bridging the gap between the human and virtual world, the need to secure your identity in the virtual world is becoming more complex and significant. The increased sophisticated attacks corner you to become vulnerable to data theft. In focus with curbing Identity-related attacks such as spray, reply and phishing, Microsoft has introduced a new feature “Security Defaults” which promises to take care of your basic security requirements.
Enabling Security Defaults through your Azure portal.
- Sign in to the Azure portal as a Security Administrator, Conditional Access Administrator, or Global Administrator.
- Browse to Azure Active Directory > Properties.
- Select Manage Security Defaults.
- Set the Enable Security Defaults toggle to Yes.
- Select Save.
or you can use this direct link to enable security defaults.
Pre-configured Security Settings in Security Defaults.
Security Defaults are the newly introduced basic level of security that Microsoft has developed. Security Defaults secures your organization through its pre-configured security settings such as: –
- Unified Multi-Factor Authentication Registration.
- Multi-Factor Authentication Enforcement.
- Blocking Legacy Authentication.
- Protecting Privileged Actions.
Unified Multi-Factor Authentication Registration.
Unified Multi-Factor Authentication Registration involves registration for Multi-Factor Authentication. You can deploy MFA through the following ways mentioned below.
- A push notification or verification code from Microsoft Authenticator Application.
- A hardware token such as OAUTH tokens can be used instead of Microsoft Authenticator Application however, you will require Azure Premium P1 or P2 to utilise them. The OATH tokens resolve the MFA issue for the users who do not have a mobile.
- It is significant to note than more than one MFA can be deployed for verification at a time, in such scenarios either OTP from Microsoft Authenticator Application or OTP from OAUTH tokens can be used.
Having difficulties with remembering your passwords.
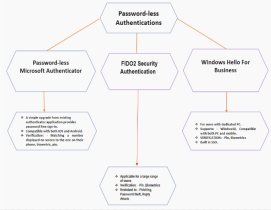
Looking for a way to go Password-free.
Here are some methods that you can adopt for password-free MFA
Multi-Factor Authentication Enforcement
Protecting Administrators:
- All significant azure ad admins will have to perform additional security authentications every time they sign-in.
Protecting All Users:
- All the users are mandatorily enabled with MFA and are prompted with additional authentication whenever necessary.
Blocking Legacy Authentication:
- Any legacy authentications protocols used by an application excluding Exchange ActiveSync will be blocked when you enable Security Defaults.
Protecting Privileged Actions:
- Users accessing Azure portal, Azure PowerShell, or the Azure CLI will need to complete additional authentication,this policy comprehensively applies for all the users with no regards to their role.
- It is significant to note that after enabling Security Defaults there will be no 14-day MFA period that will be provided for the admins.
Why Security Defaults? Why now?
With Microsoft introducing Security Defaults which has the same functionalities that the Baseline Policy had the question why is it being introduced as a new feature in the name of Security Defaults is a natural doubt that you may have and the answer to your doubt lies in the very word “Security Defaults” itself, unlike baseline policy in Security Defaults the basic security settings are enabled by default for all new users which strengthens the features ultimate goal that all the accounts must be equipped with basic security settings until they are ready to tailor their own identity security story.
Security Defaults is easy to implement and is equipped with pre-configured settings to protect your organisations account from preventable compromises with just a swipe on Security Defaults toggle.
- The major reason to introduce Security Defaults was due to the concerning telemetry that more than 99 % of attacks are targeted on end-users which can be prevented by using MFA, though this feature has been available previously it was found that only 9% of the users were availing it thereby it became significant for Microsoft to mandate MFA in Security Defaults.
- It is crucial to note that there are no options for exclusion of users in regards with these pre-configured security settings, once Security Defaults option is enabled, all these pre-configured settings are applied without any exclusion.
New users
- If you are a new user, the Security Defaults feature is enabled by default for you however, it is not observed to be true across all the tenants.
Existing users
- If you are an existing user, make sure none of your application is using legacy authentication.
- Make sure all the users in your organisation comply to register for MFA within 14 days. For detailed information on various deployment considerations and techniques in Security Defaults check out deployment considerations for Security Defaults blog.
How distinguished is Security Defaults from Baseline Policy?
The above question only corners us to realize and question, if Security Defaults is Baseline policy wrapped in different pre-configured security titles, only deprecating the feature of user exclusion?
“Security Defaults provide secure default settings that we manage on behalf of organizations to keep customers safe until they are ready to manage their own identity security story”
From the above statement, we can reflect that Security Defaults can only be fruitful to newbie users who are more concerned about setting up the necessary applications in relevance with their organisational needs than security for such users Security Defaults provides maximum protection against threats and prevents common security attacks.
Meanwhile for sophisticated users who have customization need and requirement for user exclusion especially from certain pre-configured settings in Security Defaults will have to configure Conditional Access Policy as per their organisations requirement.
While Baseline Policy did offer all the basic security protection policies as Security Defaults does, it allowed the users to enable baseline policies you require individually and provided you with user exclusion options that could be advantageous in the light of providing the capability of break glass process for privileged accounts and exemption for service accounts. After the deprecation of the Baseline Policy, the only way to avail user exclusion capabilities is by setting up a Conditional Access Policy.
Pros of Security Defaults
- If you are a new user Instead of configuring multiple security policies Security Defaults provides you maximum protection through its pre-configured security settings.
- Its free for all license levels and trial tenants.
Cons of Security Defaults
- These settings are not customizable, you can either deploy all the pre-configured security settings by selecting Security Defaults single toggle switch or disable it and configure Conditional Access as per your requirements.
- If you enable Conditional Policy, you won’t be able to subscribe to Security Defaults.
- Admins must be alert and mindful about Security Defaults update, as it has no customization possibilities thus users will be impacted by new inclusions.
The Vulnerability
As stated in Microsoft Tech Community blog on “Introduction to Security Defaults”
“We will expand first to apply Security Defaults to all new tenants as well as applying it retroactively to existing tenants who have not taken any security measures for themselves”
The above statements do not provide us clear insight as to what will be the plight of the users who had previously resorted to baseline policy and on the deletion of them, how will they be impacted. Since we do not find any documentation specifying that Security Defaults will be enabled by default for the tenants relying on Baseline Policy for protection, there lies a possibility that those users might become vulnerable as they will be ripped off the baseline protection policies that had guarded them. Thereby it is advisable to pre-configure the required policies through Conditional Access Policy or enable Security Defaults before depreciation of Baseline Policy.
Can we expect more pre-configured settings to be included in Security Defaults in the near future?
Yes!! Since Microsoft promises to judiciously expand these Security Defaults to maximize protection for the users and terms MFA as the starting point in this journey, you surely can expect more pre-configured settings to be added to Security Defaults.
Summary
With Baseline Policy deprecated on February 29th, 2020 we can’t term the transition to Security Defaults to be a smooth one since it has quite an impact on the users, essentially because Security Defaults does not have any user exclusion and if a user wants to continue to experience the same security privilege that they accustomed while baseline policy was enabled they will have to configure similar baseline policies from scratch through Conditional Access Policies and it is also required that you will have to buy Azure P1 licence to exercise customized Conditional Access Policy that they create.