Microsoft 365 audit logs maintain activities performed by both admins and users to track security breaches and suspicious activities. Large organizations generate a plethora of audit data for a short period. Due to excessive logs, security breaches are often unnoticed for a week or month or never uncovered.
Here Office 365 alerts and alert policies come in!
Office 365 Alert Policies:
Alerts are generated when the user performs activities that match the conditions given in the alert policy. With alerts, admins can take immediate actions and improve the response time for the security breach.
Microsoft provides an alerting feature to track unusual activities and identify potential threats. Alert policies can be managed through Purview compliance center or Microsoft 365 Defender portal.
But native Office 365 alerting has downsides,
High licensing cost: With E1/F1/G1, E3/F3/G3, you can use basic alerting functionality. Advanced functionality is only available in E5/G5 or with audit add-on subscriptions.
Lack of functionality: Even with advanced alerting, triggering alerts by comparing events trends (compare and analyze activities with past behavior) is not available.
Limited activities under control: With Microsoft’s alert policies, you can get alerts for limited activities. Also, it varies based on the subscription plan you have.
How AdminDroid Outperforms Native Alerting?
AdminDroid Office 365 alerting tool specially designed to enhance Microsoft 365 alerting experience with unique and intelligent features. Apart from this, AdminDroid has plenty of advantages over the native alerting system.
Reduced license cost: You don’t require E5 or any additional add-on to stay informed with alerts.
Monitor extensive activities: With AdminDroid, you can get email alerts on 1400+ Microsoft 365 activities.
A smart way to detect anomalies: You can compare and analyze all activities with past behavior. It will reduce the complication of manually defining a threshold.
Get granular alerts using ‘Scope’: Instead of org-wide alerts, you can generate property-specific alerts.
Improvise alert policies easily: Alerts Preview Console helps you generate sample alerts by examining your organization’s audit data. It will help you set up an ideal condition for an alert policy.
Create quick alert from Audit reports: AdminDroid has 600+ audit reports. You can create a quick alert policy from audit reports.
Get an overview of configured alert policy: Easily get an alert policy execution detail, such as recent execution time, next execution time, last alert time, and policy created & last modified time.
Default alert policy template: AdminDroid has 48 alert policy templates that are recommended for all organizations to identify unusual activities.
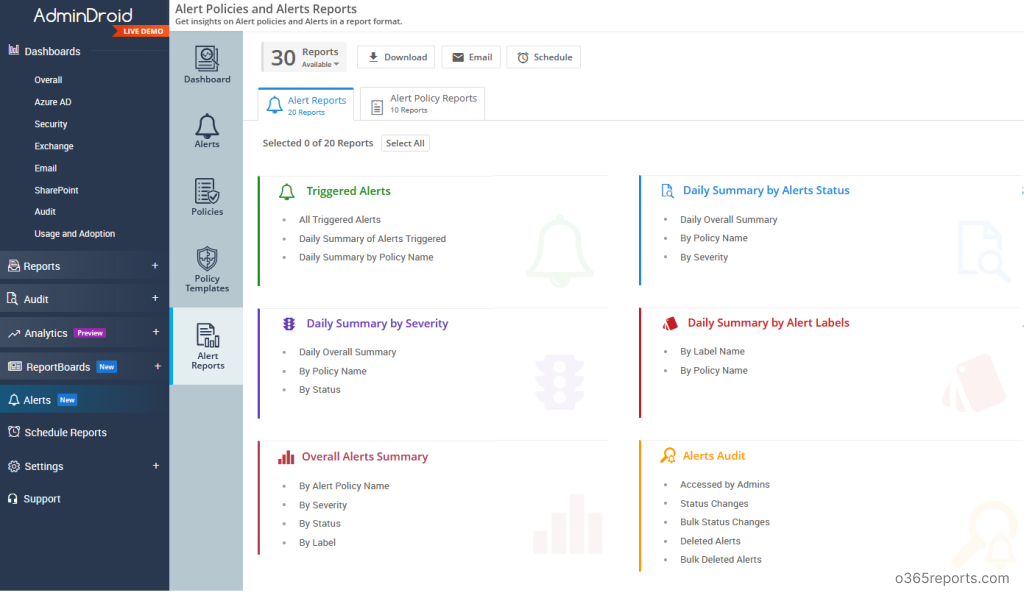
Alert policies and alert reports: You can get insights on alert policies and alerts in a report format to view them in great detail.
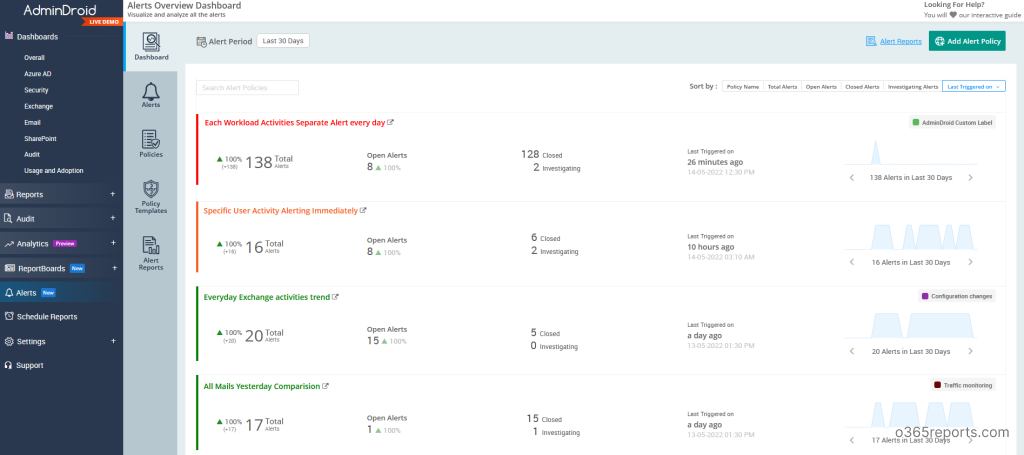
Alert dashboard: You can visualize the alerts, status, and trends swiftly with the help of the alert’s dashboard.
Multi-tenant support: You can easily manage alerts for multiple tenants using a single portal.
You can Download AdminDroid by clicking here
Protect your Organization with Security Alerts:
AdminDroid helps admins protect their organization from security threats by monitoring unusual activities and detecting anomalies. With the AdminDroid Office 365 alerting tool, you can
- Create a new alert policy
- View and take action on triggered alerts
- Visualize and analyze all the alerts using the Alerts overview dashboard
- Get insights on alerts and Policies in a report format
- Utilize ready to deploy alert policy templates.
Create a New Alert Policy:
In general, alert policies contain rules and conditions in which alerts should be triggered. With AdminDroid, you can configure alerts based on the following criteria and send alert notifications.
- New events: These alerts are triggered when a specific activity happens in an organization. E.g., external file sharing, assigning admin privileges, etc.
- Unusual events: By setting a threshold value, you can define how many times the activity has to occur before triggering an alert. It will be helpful to track unusual external user activity, bulk file deletions, etc.
- Compare events trends: This is one of the unique features of AdminDroid, which helps to compare the activities of past period patterns. The past period includes yesterday, the same day of last week, last month, etc. This method is effective in tracking unusual mail traffic, password reset trends, etc.
- Granular alerts by scope: Instead of getting an org-wide alert, you can trigger alerts only for specific attributes, such as user name, workload, file, etc. For example, instead of getting alerts for org-wide five login failures in 10mins, you can focus on a specific user (I.e., global admin account -John). When John encounters five failed login attempts in 10 mins, AdminDroid will trigger a security alert.
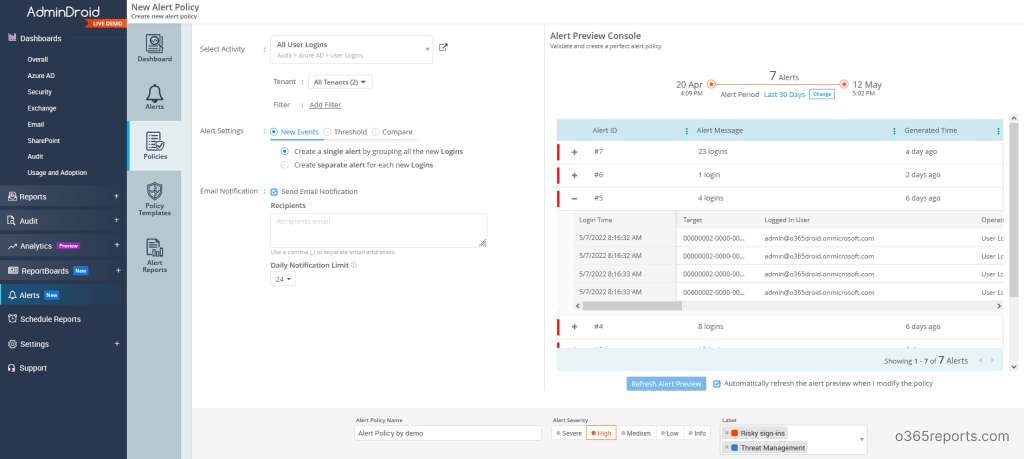
Validate Alert Policies with the ‘Alert Preview Console’:
AdminDroid’s alert preview console helps you validate and create a perfect security alert policy for your Microsoft 365 environment. The console will show the recent possible alerts from your organization’s audit data, which will help setting an ideal condition or threshold for the alerts.
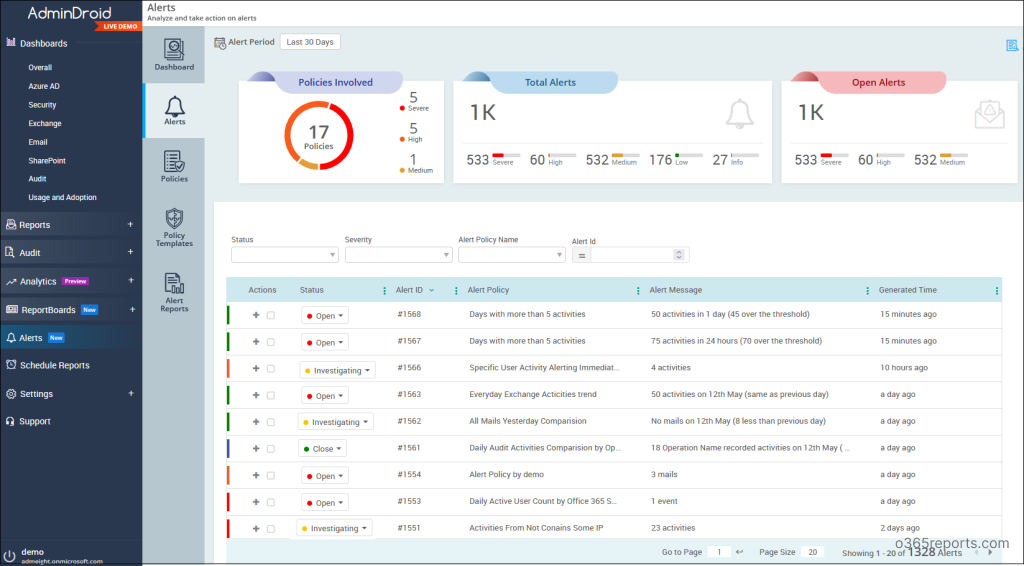
View and Take Actions on Triggered Alerts:
When a user performs an activity that matches an alert policy, alerts are triggered. You can view the generated alerts in the ‘Alerts’ tab & take necessary actions, and mark them as ‘closed’ or ‘under investigation’ based on the status.
You can also get a quick overview of policies involved, total alerts based on their severity, and open alerts based on their severity.
Visualize Alerts using Alerts Overview Dashboard:
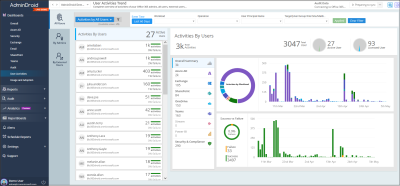
With the alerts dashboard, you can visualize and analyze all the alert policies and their triggered alerts with the alert status. It will be helpful to monitor alert policies and responses taken for the respective alerts. You can modify the ‘Alert period’ time to view the dashboard data for a custom period. Also, you can navigate to respective alert policies with a single mouse click.
Get Insights on Alert Policies and Alerts in a Report Format:
You can view the info and statistics of both configured alert policies and triggered alerts in a report format from a single interface. You can export the report in multiple formats, such as HTML, PDF, CSV, XLS, XLSX, and RAW. Additionally, you can schedule or email the reports.
Utilize Ready to Deploy Alert Policy Templates:
AdminDroid provides 45+ build-in alert policies that are recommended for all organizations to identify elevation of admin privileges, external sharing, email traffic monitoring, risky sign-ins, etc. Each template will show the possibility of alerts by analyzing your existing audit data. By previewing the default policy in the advanced ‘Alert preview console’, you can add or modify filters and deploy the alert policies.
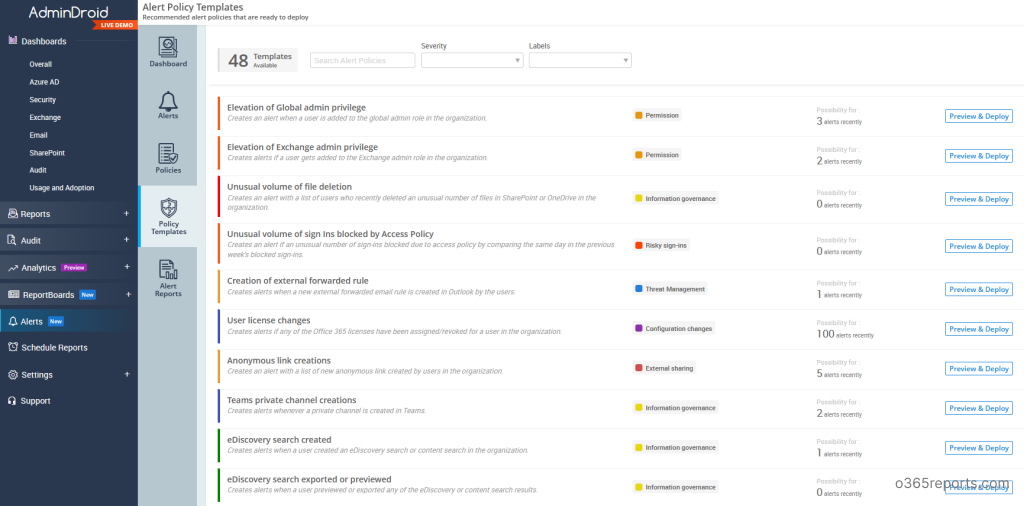
AdminDroid Office 365 alerting tool offers the following default alert policies in the given categories.
Threat Management
- Creation of external forwarding rule
- Malware campaign detected after delivery
- Admins forced user password reset
- Anti-phish policy creation and changes
- Unusual anonymous user file activities
- Unusual volume of users’ daily login failure summary
- All failed activities
- Resolved risky sign-ins of users
- Blocked user attempted to login
- Unusual volume of downloading activities
Risky Sign-ins
- Unusual volume of sign-ins blocked by Conditional Access policy
- High level risky sign ins
- Unusual volume of admins’ login failures
- Unlikely travel risk detections
- Sign ins from anonymous IP address
- Admin confirmed user compromised
- Unusual user login failures
- users’ risky sign-ins with detailed information
- All confirmed risky sign-ins
External Sharing
- Anonymous link creation
- Unusual volume of external file sharing
- Unusual external user file access activity
- Resource accessed using anonymous links
- Unusual number of site invitations shared to external users
Information Governance
- Unusual volume of file deletion
- Teams private channel creation
- eDiscovery search created
- eDiscovery search exported or previewed
- Unusual volume of anonymous link creation
- Accessed notes in OneNote by comparing current week with previous week
- Accessed OneDrive files by comparing current week with previous week
- Accessed SharePoint files by comparing current week with previous week
- SharePoint DLP rule matched documents
- File sharing by external users via Teams channel
Traffic Monitoring
- DLP rule detected mails
- Mail flow configuration changes
- Mailbox non owner access
- Sign-ins based on application
Permission
- Elevation of global admin privilege
- Elevation of Exchange admin privilege
- Admin consent to applications
- Elevation of administrative privilege
- Teams channel ownership changes
- Re-enabling blocked user accounts
- SharePoint sharing policy changes
- Users removed from Admin role permissions
Configuration Changes
- User license changes
- Advanced Threat Protection configuration changes
- Directory settings changes
- Domain changes
- Data Loss Prevention configuration changes
- ATP default policy changes
- MFA disabled users
- Group owner changes
- License assigned to external users
- Disabling O365 audit logging
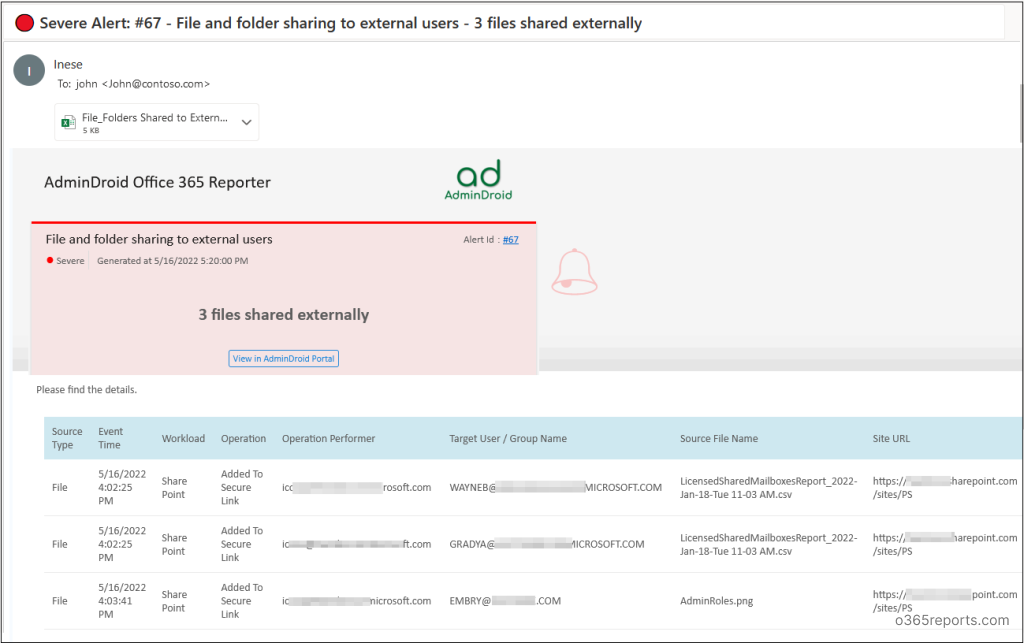
Office 365 Alert Notification – Sample:
AdminDroid sends detailed alert email notification to the configured recipients. The email notification contains all the events in the message body. Also, the activities’ details are attached as a report; you can download it and analyze suspicious activities.
Conclusion:
‘AdminDroid Microsoft 365 monitoring and alerting tool’ provides more features to enhance your real-time alerting experience. You can directly download AdminDroid Office 365 alerting tool from their website to explore its capabilities. Establish an effective alerting with AdminDroid’s unique and intelligent features. Happy alerting!
Do I need to say more?! See it in action: https://demo.admindroid.com/