Within this increasingly digital world, ensuring security🔐 is a major challenge for worldwide organizations. To address this concern, Multi-Factor Authentication (MFA) stands as an invincible shield, fortifying Microsoft 365 with multi-layered protection. While MFA management provides robust security for Microsoft 365, it is equally essential to have an authentication technique for Azure apps. Hopefully, some methods including client secret authentication, facilitate a handshake with the Azure app’s authentication process. This interesting blog takes you through the ins and outs of client secret management in Azure AD, unlocking the secrets to protect your applications and prepare you against digital threats.
Let’s explore🔎 the core of secure authentication and uncover the true power of Azure AD’s client secret management.
“Cyber-Security is much more than a matter of IT”
– Stephane Nappo
What is Client Secret in Azure AD?
A client secret is an authentication technique that uses a string value in the Azure application instead of a certificate for identity. It is also called an application password that is used for the authentication of tokens for Azure app access. The Azure AD issues a token to access the desired resource upon successful verification of the client secret.
Warning: Due to the challenges of secret storage, it is considered less secure than certificate-based authentication. Certificate credentials are considered as high-security environments for their enhanced security features.
Client Secret Management in Azure AD
The steps below allow you to manage the client secret for an application in the Azure AD portal. You can adhere to the appropriate management operation concerning your need. First, make sure to login into the Microsoft Entra admin center.
- Get Client Secret from Azure App Registration
- Create an Azure Client Secret for Applications
- Create Client Secrets in Azure AD Using PowerShell
- Check and Update Client Secret Expiry in Azure AD
- Delete a Client Secret from an Azure App
Get Client Secret from Azure App Registration
To generate a client secret for an Azure application, you need to follow the procedure below within the Microsoft Entra admin center.
1. Head to the “Identity” tab and choose “Applications”.
2. Select “App registrations” under the “Applications” tab.
3. Select the desired application where you want to view the client secret configuration.
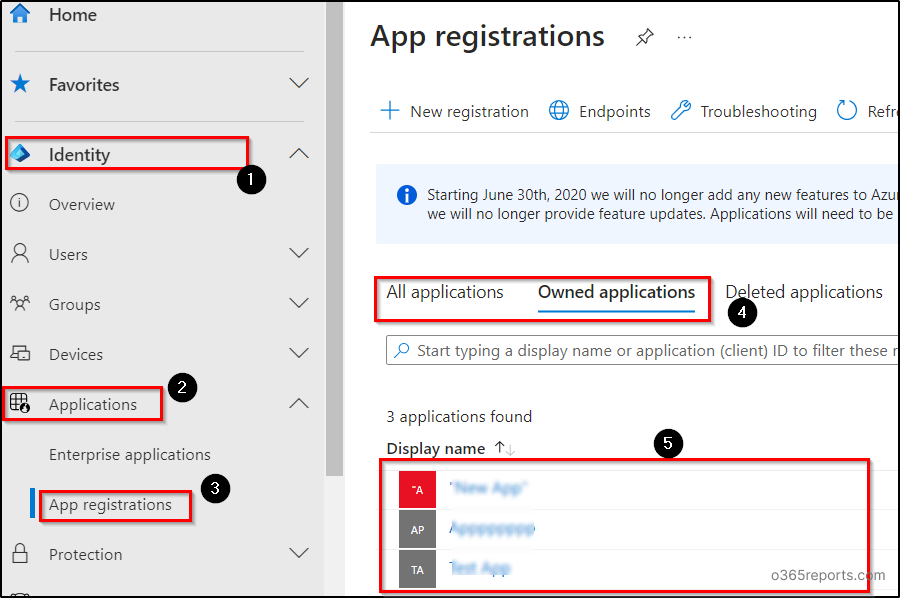
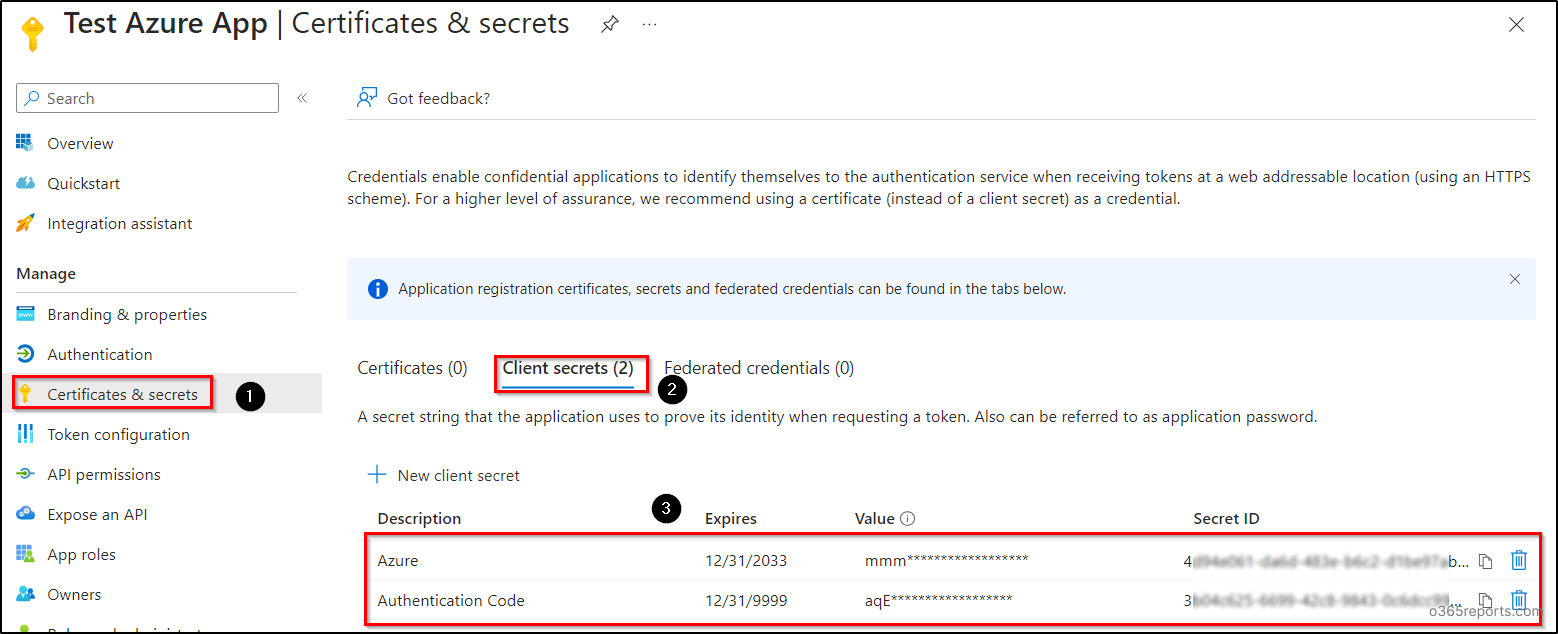
4. In the respective application menu, select the “Certificates & secrets” tab.
5. You can see the list of client secret configurations in the “Client secrets” tab.
Create an Azure Client Secret for Applications
To create client secrets for an Azure app, navigate to the “Client secrets” tab as discussed above and follow the below steps.
1. Click on the “New client secret” button and input an appropriate description for the client secret.
2. Choose the expiry date in the drop-down and click on the “Add” button. Here, you can specify a maximum of 24 months for the expiration of client secrets within the Azure portal. But with the help of PowerShell, you can set the expiration beyond 24 months.
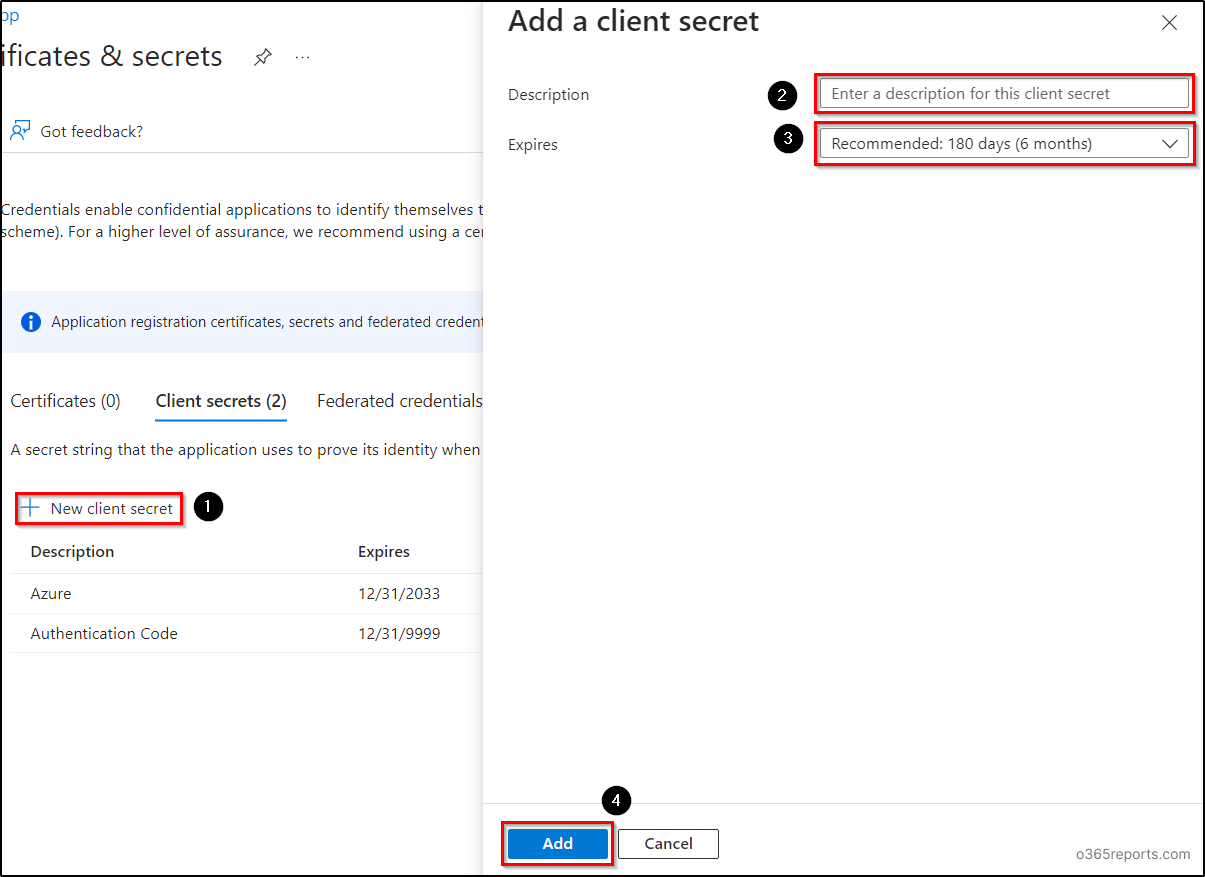
Note: After the successful creation of the client secret, copy the “Value” of the secret and keep it for future activities. The client secret value will disappear once the page is refreshed. This value may be needed for periodic authentication, token renewal, key vault linking, and more.
Create Client Secrets in Azure AD Using PowerShell
You can use the below PowerShell cmdlet to create client secrets in Azure Active Directory for more than 2 years or without expiration (up to the year 9999). Before executing the cmdlet make sure to connect to Microsoft Graph PowerShell with the scope “Application.ReadWrite.All”.
|
1 2 |
Add-MgApplicationPassword -ApplicationId <AppObjectId> -PasswordCredential @{ DisplayName=<ClientSecretDescription>; EndDateTime=[DateTime]::ParseExact("12/31/9999","MM/dd/yyyy",$null)} |
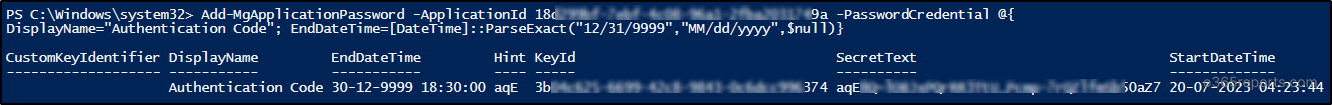
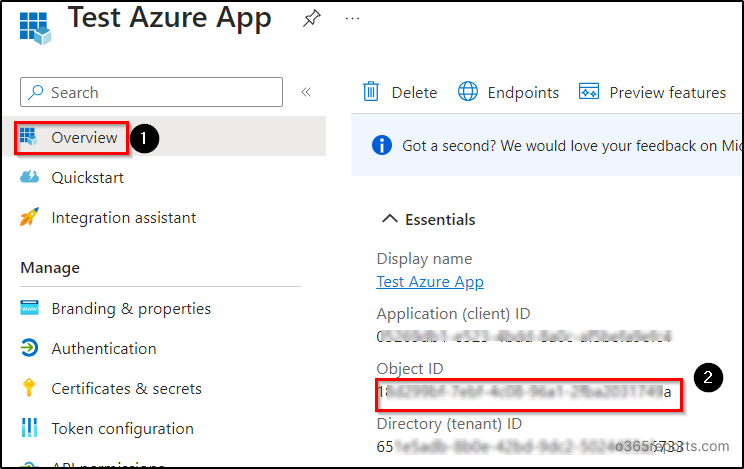
Replace <AppObjectId> with the corresponding object Id of the Azure AD application and “12/31/9999” with an appropriate expiry date. You can get the object Id from the “Overview” page of the respective app. Also, replace <ClientSecretDescription> with the corresponding description of the client secret.
Note: You can also block the creation of client secrets or set a default expiry lifetime for client secrets across all apps or specific apps using Microsoft Entra application management policies.
Check and Update Client Secret Expiry in Azure AD
If the client secret expires, users can’t access or sign in to the application portal and will see an error page. In the Azure portal, you can verify the client secret’s expiration on the “Client secrets” page. If a certificate is expired, the message saying, “A certificate or Secret is expired. Create a new one” will be displayed in the Azure portal.
In case of expiry, a fresh client secret can generated in the Azure portal (maximum of 2 years) or using PowerShell (long period). However, please note that this secret cannot be renewed beyond its expiration date. To proactively manage this, you can use the apps with client secrets report to get all the Entra applications that have secrets in your Microsoft 365 environment.
Note: Once you create new secrets in case of expiration, make sure to update the configuration or application code to use the new one.
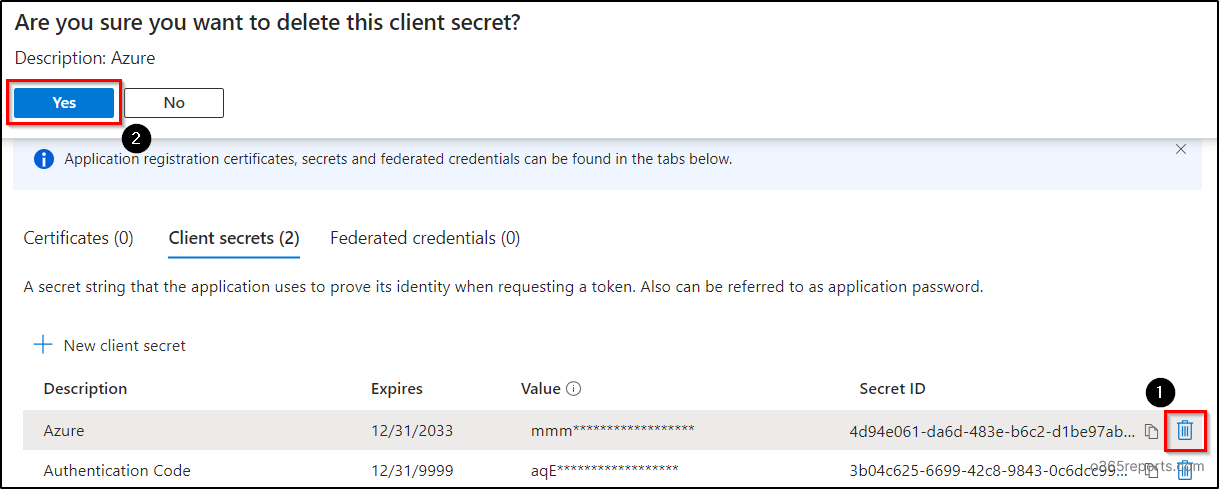
Delete a Client Secret from an Azure App
In some rare cases, it is essential to delete client secrets to prevent unauthorized access to your resources. It is also necessary to delete the client secret after it has expired. To delete client secrets, use the delete icon located with the respective client secret on the “Client secrets” page and select “Yes”.
Alternatives for Client Secrets Authentication
Besides the client secrets, the Azure Active Directory offers two inbuilt protection strategies to safeguard the applications. The other two alternatives are:
Certificate-Based Authentication: In Azure app authentication, certificates are referred to as public keys. This certificate proves the identity of the application with secrets when users request to access the app. For example, you can connect to Microsoft Graph PowerShell using certificate authentication instead of admin authentication.
Federated Credentials Authentication: Incorporating a trust with an external OIDC-Open ID connect, federated credentials allow other identities to impersonate applications. Federated authentication allows you to get tokens to access Azure and Microsoft Graph.
I hope that the blog has provided you with an overview of client secret management in Azure AD to optimize security. Feel free to leave your queries in the comments section. We are happy😄 to help you. Stay tuned!